[ad_1]
The Linux and FreeBSD operating systems contain newly discovered vulnerabilities that make it easy for hackers to remotely crash servers and disrupt communications, researchers have warned. OS distributors are advising users to install patches when available or to make system settings that lower the chances of successful exploits.
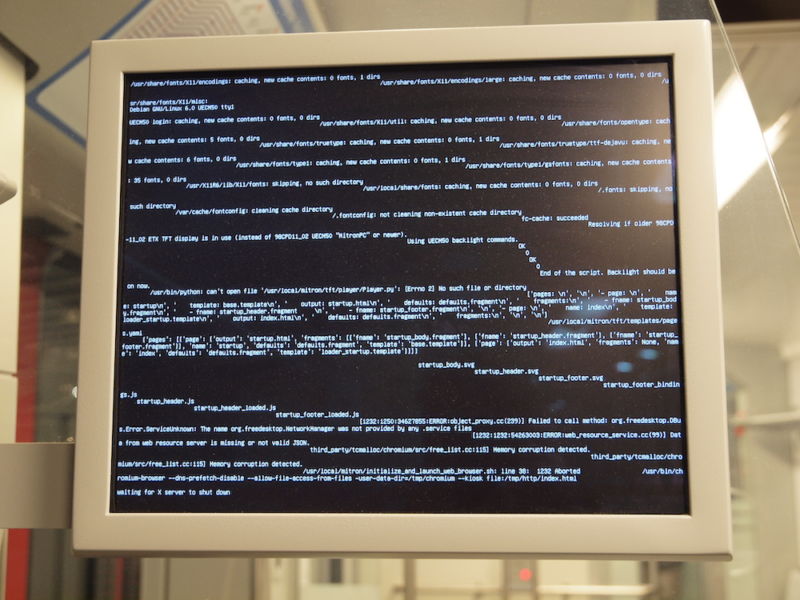
The most severe of the vulnerabilities, dubbed SACK Panic, can be exploited by sending a specially crafted sequence of TCP Selective ACKnowledgements to a vulnerable computer or server. The system will respond by crashing, or in the parlance of engineers, entering a kernel panic. Successful exploitation of this vulnerability, tracked as CVE-2019-11477, results in a remote denial of service (DoS).
A second vulnerability also works by sending a series of malicious SACKs that consumes computing resources of the vulnerable system. Exploits most commonly work by fragmenting a queue reserved for retransmitting TCP packets. In some OS versions, attackers can cause what’s known as an “expensive linked-list walk for subsequent SACKs.” This can result in additional fragmentation, which has been dubbed “SACK slowness.” Exploitation of this vulnerability, tracked as CVE-2019-11478, drastically degrades system performance and may eventually cause a complete DoS.
Read 5 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
- Probable Russian Navy covert camera whale discovered by Norwegians
