[ad_1]
Enlarge / A graphical depiction of Thursday’s BGP leak. (credit: ThousandEyes)
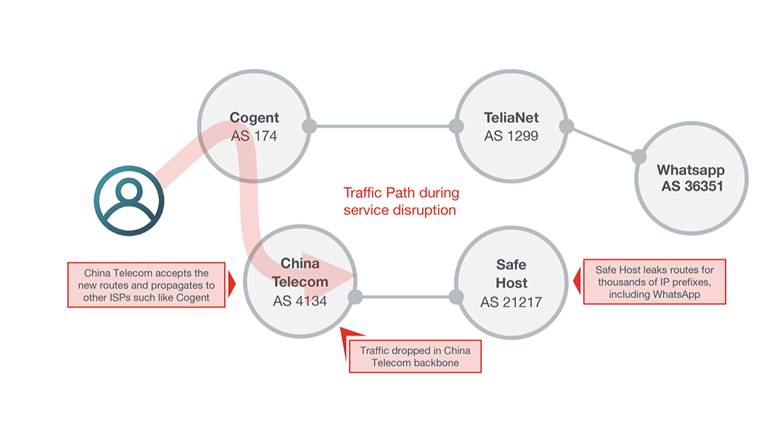
Traffic destined for some of Europe’s biggest mobile providers was misdirected in a roundabout path through the Chinese-government-controlled China Telecom on Thursday, in some cases for more than two hours, an Internet-monitoring service reported. It’s the latest event to stoke concerns about the security of the Internet’s global routing system, known as the Border Gateway Protocol.
The incident started around 9:43am UTC on Thursday (2:43am California time). That’s when AS21217, the autonomous system belonging to Switzerland-based data center colocation company Safe Host, improperly updated its routers to advertise it was the proper path to reach what eventually would become more than 70,000 Internet routes comprising an estimated 368 million IP addresses. China Telecom’s AS4134, which struck a network peering arrangement with Safe Host in 2017, almost immediately echoed those routes rather than dropping them, as proper BGP filtering practices dictate. In short order, a large number of big networks that connect to China Telecom began following the route.
The result: much of the traffic destined for telecommunications providers using the affected IP addresses passed through China Telecom equipment before either being sent to their final stop or being dropped during long waits caused by the roundabout paths. Traceroutes taken by Doug Madory, a security analyst at Oracle who first reported the leak, show just how circuitous the paths were. The following screenshot shows traffic starting at a Google Cloud server in Virginia passing through China Telecom’s backbone network before finally reaching its intended IP address located in Vienna, Austria.
Read 14 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
- Probable Russian Navy covert camera whale discovered by Norwegians
