[ad_1]
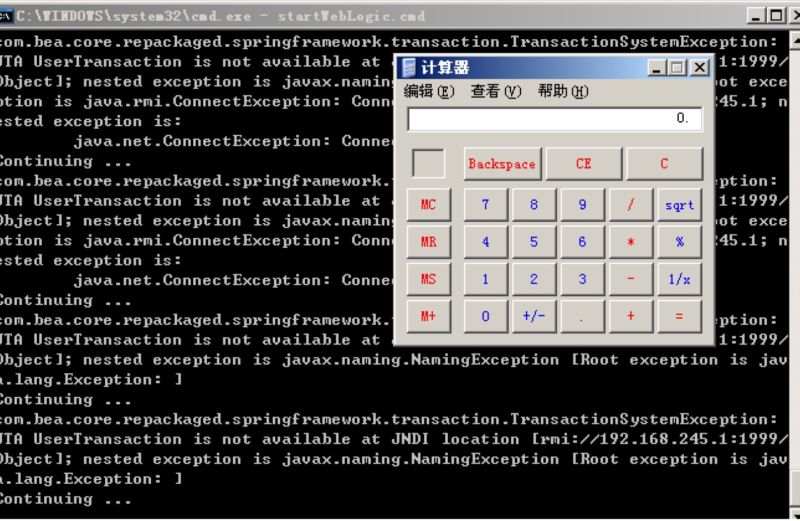
Enlarge / Security team KnownSec404 proof-of-concept image, showing an instance of Windows Calculator being run on the remote WebLogic server. (credit: KnownSec 404)
Oracle on Tuesday published an out-of-band update patching a critical code-execution vulnerability in its WebLogic server after researchers warned that the flaw was being actively exploited in the wild.
The vulnerability, tracked as CVE-2019-2729, allows an attacker to run malicious code on the WebLogic server without any need for authentication. That capability earned the vulnerability a Common Vulnerability Scoring System score of 9.8 out of 10. The vulnerability is a deserialization attack targeting two Web applications that WebLogic appears to expose to the Internet by default—wls9_async_response and wls-wsat.war.
The flaw in Oracle’s WebLogic Java application servers came to light as a zero-day four days ago when it was reported by security firm KnownSec404.
Read 3 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
- Probable Russian Navy covert camera whale discovered by Norwegians
