[ad_1]
Enlarge (credit: SandboxEscaper)
A serial publisher of Microsoft zeroday vulnerabilities has dropped exploit code for three more unpatched flaws, marking the seventh time the unknown person has done so in the past year.
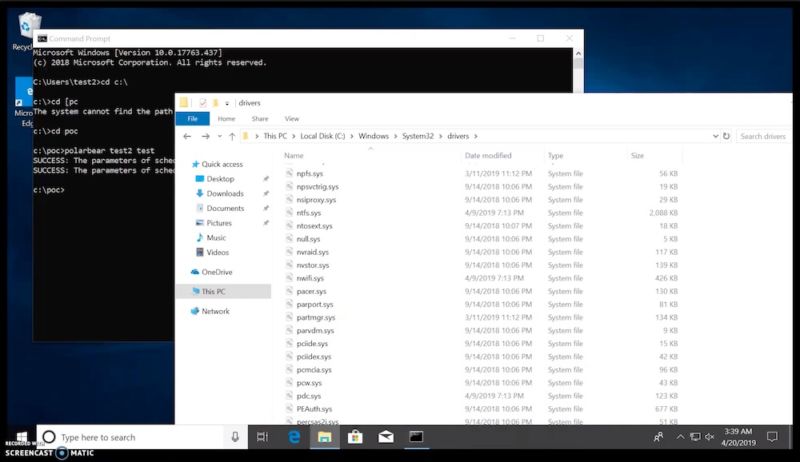
Technical details of the vulnerabilities, along with working proof-of-concept exploits, are the work of someone using the moniker SandBoxEscaper. A local privilege-escalation vulnerability in the Windows Task Scheduler that was disclosed on Tuesday allows an authenticated attacker to gain SYSTEM privileges on an affected system. On Thursday, the person released a privilege escalation code that exploits a bug in the Windows Error Reporting service. Attackers can use it to modify files that would normally be off limits. A third exploit, which was also released Wednesday, works against Internet Explorer 11 and allows attackers to execute a JavaScript that runs with higher system access than is normally permitted by the browser sandbox.
Decent deal
Like the other exploits SandboxEscaper has published over the past year—including this one Ars covered last August and this one from last October—the three recent ones don’t allow attackers to remotely execute malicious code. Still, as security defenses in recent versions of Windows and other operating systems have improved, the value of these types of exploits has grown, since they are often the only way to bypass security sandboxes and similar protections. Despite some limitations in the exploit that were transparently noted by SandBoxEscaper, the disclosures are significant if they work as purported against fully patched versions of Windows 10.
Read 5 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Systems with small disks won’t be able to install Windows 10 May 2019 update
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
