[ad_1]
Enlarge (credit: One of the slides posted to Github)
A security researcher has published a detailed guide that shows how to execute malicious code on Windows computers still vulnerable to the critical BlueKeep vulnerability. The move significantly lowers the bar for writing exploits that wreak the kinds of destructive attacks not seen since the WannaCry and NotPetya attacks of 2017, researchers said.
As of three weeks ago, more than 800,000 computers exposed to the Internet were vulnerable to the exploit, researchers from security firm BitSight said last week. Microsoft and a chorus of security professionals have warned of the potential for exploits to sow worldwide disruptions. The risk of the bug, found in Microsoft’s implementation of the remote desktop protocol, stems from the ability for attacks to spread from one vulnerable computer to another with no interaction required of end users.
“A pretty big deal”
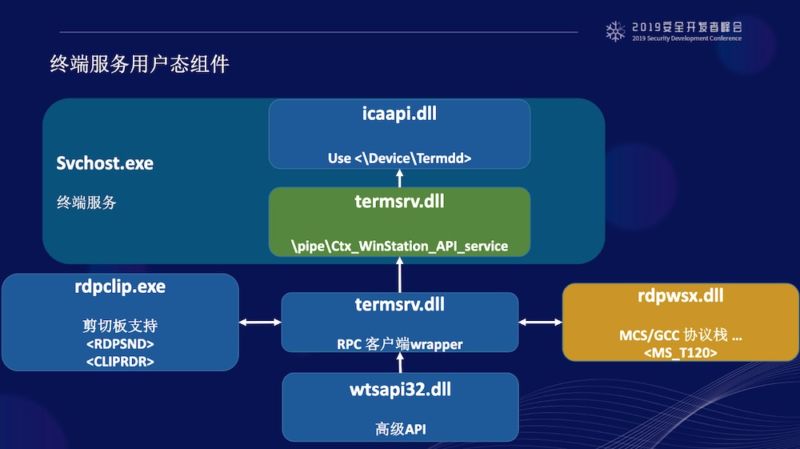
One of the only things standing in the way of real-world attacks is the expertise required to write exploits that remotely execute code without crashing the computer first. Several highly skilled whitehat hackers have done so with varying levels of success, but they have kept the techniques that make this possible secret. Much of that changed overnight, when a security researcher published this slide deck to Github.
Read 13 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Systems with small disks won’t be able to install Windows 10 May 2019 update
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
