[ad_1]
Enlarge (credit: ybierling.com)
A Korean-speaking hacking group in operation since at least 2016 is expanding its arsenal of hacking tools to include a Bluetooth-device harvester in a move that signals the group’s growing interest in mobile devices.
ScarCruft is a Korean-speaking advanced persistent threat group that researchers with security firm Kaspersky Lab have been following since at least 2016. At the time, the group was found using at least four exploits, including an Adobe Flash zeroday, to infect targets located in Russia, Nepal, South Korea, China, India, Kuwait, and Romania.
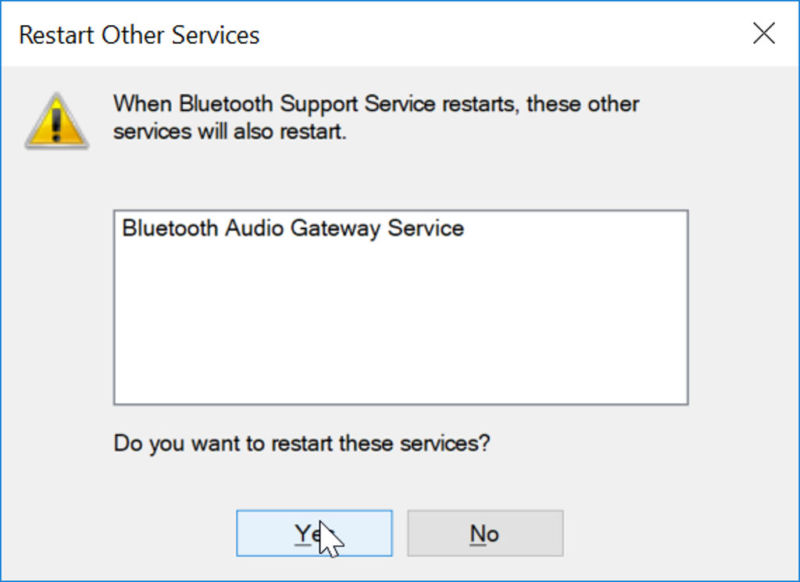
In a post published Monday, Kaspersky Lab researchers said they discovered a custom Bluetooth-device harvester created by ScarCruft. The researchers wrote:
Read 6 remaining paragraphs | Comments
[ad_2]
Source link
Related Posts
- Cox Internet now charges $15 extra for faster access to online game servers
- Comcast usage soars 34% to 200GB a month, pushing users closer to data cap
- After White House stop, Twitter CEO calls congresswoman about death threats
- The sim swap the US isn’t using
- Probable Russian Navy covert camera whale discovered by Norwegians
